Key Takeaway:
Rogue websites use typosquatting, homograph attacks, and AI-generated copy to impersonate brands. The top threats include fake login portals, “hype-based” product launches, counterfeit stores, fraudulent support pages, and supply chain impersonation
Rogue websites use typosquatting, homograph attacks, and AI-generated copy to impersonate brands. The top threats include fake login portals, « hype-based » product launches, counterfeit stores, fraudulent support pages, and supply chain impersonation.
Every day, customers open login pages identical to your corporate portal. They receive urgent updates from « support » pages offering help with their account. Investment platforms promise unbelievable returns, and shopping websites burst with luxury deals in your brand’s name. The devastating truth is, any one of them could be rogue websites or fake pages.
These rogue websites exist solely to steal credentials, drain bank accounts, and trick unsuspecting employees, consumers, and partners. They erode trust, devastate brands, and inflict massive financial losses.
In this guide, we’ll dissect the top five tactics to target US businesses with fake webpages. You can also check which rogue websites are spoofing your organization for free right here.
What Exactly is a Rogue Website?
The term “Rogue websites” covers malicious and fraudulent web pages that impersonate legitimate brands, services, or individuals. Websites go rogue when cybercriminals exploit lax domain registration processes to secure deceptive URLs (e.g., amaz0n-support.com or microsoft-security-alert.net). They use tactics like typosquatting, homograph attacks, and hijacked subdomains to secure deceptive infrastructure. Once registered, they build their fake pages with nuanced and specific strategies to trick their targets. Increasingly, they’re so effective in their impersonations that even digital authorities like ICANN can no longer tell which is which.
| Tactic | Primary Target | Security Impact |
|---|---|---|
| Fake Logins | Corporate Staff / HR | Credential Theft & Breach |
| Product Hype | Investors / Superfans | Financial & Crypto Fraud |
| Fake Stores | General Consumers | Credit Card & Data Theft |
| Support Pages | Account Holders | Remote System Hijacking |
| Supply Chain | B2B Partners / Suppliers | Invoice Fraud & BEC Scams |
Cybercriminals dress their rogue websites in stolen logos, brand colors, and AI-generated copy that mirrors legitimate communications. Deceptive landing pages often leverage SSL certificates (showing the « padlock » icon) to appear secure, exploiting user trust. Once live, they slowly and steadily implement scams and cybercrimes like fraud, counterfeiting, and data theft.
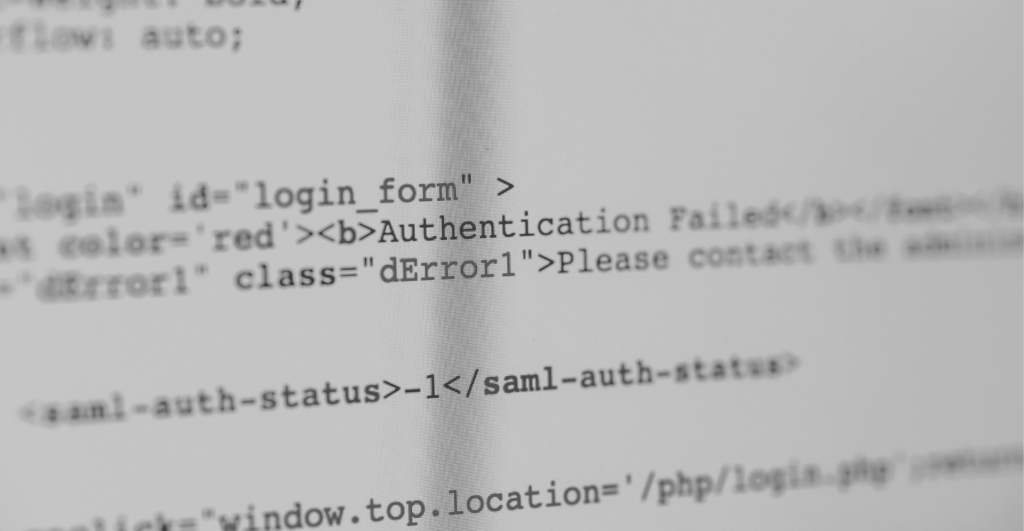
Tactic 1: Fake Login Pages + Phishing Emails
The most devastating rogue website attacks occur right at the start of your digital journey: your inbox and your login page. Attackers deploy deceptive pages that mimic login portals across the internet. They spoof customer login pages, and internal platforms like VPN access or payroll systems. Scammers recently hosted fake login pages for platforms like Netflix that were so convincing that authorities had to step in. Armed with the latest phish kits like Darcula 3.0, criminals have your infrastructure in their sights.
Tactic 2: Promotions & Product Launches on Rogue Websites
Scammers exploit the hype around product drops by creating rogue websites that impersonate well-known brands. Worse, they impersonate CEOs and celebrities on social media to leverage reputations. Fake tweets or LinkedIn posts drive traffic to scam sites selling nonexistent products, « exclusive » NFTs, or fraudulent investments. These rogue websites use polished designs, fake countdown timers, and stolen media to appear authentic.
Within the broader issue of phishing, VIP impersonation runs rampant. Exploring VIP and Executive Protection solutions also helps organizations secure their online footprint, and protect their clients as well as their business leaders.
Tactic 3: Fake Online Stores Exploiting Events
Fraudulent sites impersonate legitimate stores, offering « too-good-to-be-true » discounts, exclusive launches, or liquidation sales. For example, when craft retailer Joann faced financial struggles, scammers launched rogue websites posing as official « going-out-of-business » sales. While they operate year-round, these scams seem to grab headlines during ecommerce surges like shopping seasons, preying on urgency and consumer trust. They also violate intellectual property laws by illegally using trademarks, copyrighted images, and brand names.
Tactic 4: Fake Support Pages on Rogue Websites
Cybercriminals build rogue websites mimicking essential teams like IT support, helplines, or account management. Using stolen contact lists from breaches or dark web sales, they blast communication channels. SecurityWeek recently reported that these kinds of scams targeted all kinds of large US companies, from Apple to Bank of America.
Tactic 5: Rogue Supply Chain & Partner Portals
Attackers impersonate trusted partners like suppliers, resellers, or recruiters with fake websites portals for invoices, contracts, and project updates. In one recent scheme, scammers sent convincing emails posing as Meta recruiters, directing victims to fraudulent domains.

The consequences extend far beyond financial loss. Fake recruitment portals erode trust in corporate hiring processes. These threats demand continuous domain monitoring, strict third-party verification protocols, and employee training to recognize these sophisticated deceptions.
Conclusion: Don’t Let Rogue Websites Win
When scams blend fake sites with email, social media, and even deepfakes, we must take a comprehensive approach to fighting back. With the right strategy, you can hunt down impersonating domains, social accounts, and apps. Discover if your brand is being exploited right now with a Free Rogue Websites Audit. Protect your revenue, reputation, and customers today.